

The Caesar Cipher is another simplistic cipher where letters are replaced with another letter a fixed number of letters away. For instance, given a shift of three, A becomes D, Z becomes C, etc. The cipher was developed by Julius Caesar for his private/wartime messages. Today it is still one of the most popular and most well-known ciphers. The Caesar Cipher is used in other ciphers, such as the Vigenère Cipher. The Caesar Cipher's simplicity allows it to be understood and applied easily, however, that also makes the Caesar Cipher one of the weakest forms of encryption.
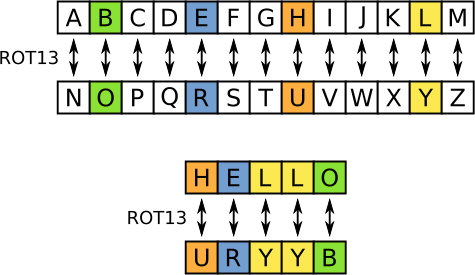
ROT13 is a special variant of the Caesar Cipher where the alphabet is shifted by 13 places. Since the alphabet is 26 letters long, ROT13 acts as its own inverse - a 13 shift encrypts, a 13 shift also decrypts. ROT13 is often used for simple encryption activities, such as on online fourms, beginner cryptology challenges, or in programs which don't require much security.
Encoding the Caesar Cipher is not relatively difficult. To start, it would be incredibly helpful to write down two alphabets: a standard alphabet, and an alphabet starting at the nth letter of the alphabet, where n is the desired shift. Then, to encrypt your text:
Decoding the Caesar Cipher is less trivial than Atbash - to decode the Caesar cipher, you must use the same method as encryption, but with a shift of 26 - n. For instance, if a text is shifted by 5, than it must be decrypted with a shift of 21.
Breaking the Caesar cipher is also rather easy - since only 25 unique shifts can occur, one could simply run through every shift manually and see which produces an comprehensible answer. This is what we call a brute-force method of breaking a cipher, since we don't eliminate possibilities using logic or deduction, but simply run through all possible solutions until a correct one is found.
Plaintext: a b c d e f g h i j k l m n o p q r s t u v w x y z
Ciphertext: N O P Q R S T U V W X Y Z A B C D E F G H I J K L M
Plaintext: CRYPTOLOGY IS COOL
Ciphertext: PELCGBYBTL VF PBBY

Example 1: Decipher IWT FJXRZ QGDLC UDM YJBEH DKTG IWT APON SDV Example 2: Decipher RFYLIQ DMP SQGLE RFGQ QGRC Example 3: Decipher MRKBQO EZ DRO RSVV KD YXMO Example 4: Decipher M GEQI, M WEA, M GSRUYIVIH Paragraph: DecipherJXUHU YI Q JXUEHO MXYSX IJQJUI JXQJ YV ULUH QDOEDU TYISELUHI UNQSJBO MXQJ JXU KDYLUHIU YI VEH QDT MXO YJ YI XUHU,
YJ MYBB YDIJQDJBO TYIQFFUQH QDT RU HUFBQSUT RO IECUJXYDW ULUD CEHU RYPQHHU QDT YDUNFBYSQRBU.
JXUHU YI QDEJXUH JXUEHO MXYSX IJQJUI JXQJ JXYI XQI QBHUQTO XQFFUDUT.